Configure Telnet/SSH Access to Device with VRF's
Introduction
This document describes the configuration of device access with Telnet or Secure Shell (SSH) across a Virtual Routing and Forwarding (VRF).
Background Information
In IP-based computer networks, VRF is a technology that allows multiple instances of a routing table to co-exist within the same router at the same time. Because the routing instances are independent, the same or overlapping IP addresses can be used without any conflict with each other. Network functionality is improved because network paths can be segmented without the requirement of multiple routers.
VRF might be implemented in a network device by distinct routing tables known as Forwarding Information Bases (FIBs), one per routing instance. Alternatively, a network device may have the ability to configure different virtual routers, where each one has its own FIB that is not accessible to any other virtual router instance on the same device.
Telnet is an application layer protocol used on the Internet or local area networks (LAN) to provide a bi-directional interactive text-oriented communication facility using a virtual terminal connection. User data is interspersed in-band with Telnet control information in an 8-bit byte oriented data connection over the Transmission Control Protocol (TCP).
SSH is a cryptographic network protocol for operating network services securely over an unsecured network. The best known example application is for remote login to computer systems by users.
Often when these technologies are used together, they create confusion, especially when you try to remotely access a device through an interface that belongs to a non global routing VRF instance.
This configuration guides uses Telnet as a form of management access just for exemplary purposes. The concept can be extended for SSH access too.
Prerequisites
Requirements
There are no specific requirements for this document.
Components Used
This document is not restricted to specific software and hardware versions.
The information in this document was created from the devices in a specific lab environment. All of the devices used in this document started with a cleared (default) configuration. If the network is live, make sure that you understand the potential impact of any command.
Configure
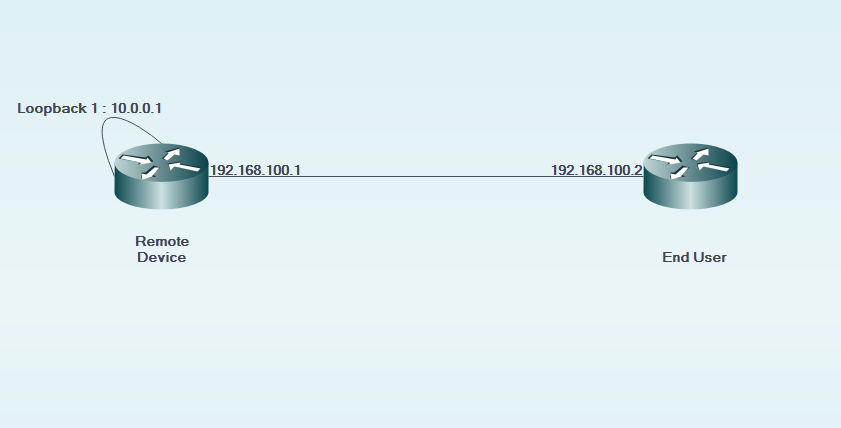
Network Diagram
Configuration
On the remote device:
! interface GigabitEthernet0/0 description LINK TO END USER ip vrf forwarding MGMT ip address 192.168.100.1 255.255.255.252 duplex auto speed auto !
! interface Loopback1 description LOOPBACK TO TELNET INTO FOR MANAGEMENT ACCESS ip vrf forwarding MGMT ip address 10.0.0.1 255.255.255.255 !
! line vty 0 4 access-class 8 in password cisco login transport input all line vty 5 15 access-class 8 in password cisco login transport input all !
On the end user:
! interface GigabitEthernet0/0 description LINK TO REMOTE SITE ip vrf forwarding MGMT ip address 192.168.100.2 255.255.255.252 duplex auto speed auto !
Verify
Use this section in order to confirm that your configuration works properly.
Before the vrf-also keyword is used in the access-class of line vty 0 15 configuration of the remote device:
EndUser#ping vrf MGMT ip 10.0.0.1 Type escape sequence to abort. Sending 5, 100-byte ICMP Echos to 10.0.0.1, timeout is 2 seconds: !!!!! Success rate is 100 percent (5/5), round-trip min/avg/max = 1/1/4 ms
EndUser#telnet 10.0.0.1 /vrf MGMT Trying 10.0.0.1 ... % Connection refused by remote host
Packet hits on the remote device increase as the ACE count that corresponds increases.
RemoteSite#show ip access-lists 8
Standard IP access list 8
10 permit 192.168.100.2 log (3 matches)
However, after the vrf-also keyword is added in the access-class of line vty 0 15, telnet access is permitted.
As per the defined behaviour, Cisco IOS devices accept all VTY connections by default. However, if an access-class is used, the assumption is that connections must arrive only from the global IP instance. However, if there is a requirement and desire to allow connections from VRF instances, use the vrf-also keyword along with the corresponding access-class statement on the
line configuration.
line configuration.
! line vty 0 4 access-class 8 in vrf-also ****This command mandatory if you use vrf directly connected device**** password cisco login transport input all line vty 5 15 access-class 8 in vrf-also password cisco login transport input all !
EndUser#ping vrf MGMT ip 10.0.0.1 Type escape sequence to abort. Sending 5, 100-byte ICMP Echos to 10.0.0.1, timeout is 2 seconds: !!!!! Success rate is 100 percent (5/5), round-trip min/avg/max = 1/1/1 ms
EndUser#telnet 10.0.0.1 /vrf MGMT Trying 10.0.0.1 ... Open User Access Verification Password: RemoteSite>
Troubleshoot
This section provides information you can use in order to troubleshoot your configuration.
VRF based troubleshooting might be needed at times. Ensure that the concerned interfaces are all in the same VRF and they have reachability within the same VRF.
Also, relevant SSH and Telnet related troubleshooting might be needed.
Comments
Post a Comment